Following article is currently available on Allahabad High Court's website :
WHO SHAVES THE BARBER:
Adjudicating Officers―Role, Implementation, Challenges
(Text of talk delivered by Justice Yatindra Singh, Judge Allahabd High Court, in the National seminar on Enforcement of Cyber Law under the 'National Project Committee on Enforcement of Cyber Law' constituted by the Hon'ble the Chief Justice of India under the Chairmanship of Hon'ble Mr. Justice Altamas Kabir, Judge, Supreme Court of India on 08.05.2010 at the Symposium Hall NASC, Pusa, New Delhi)
Does it matter as to who is the barber; or who shaves him? Does he require a shave? What matters to an adjudicating officer is―what gain has been made by a hacker; what damage has he caused; and how many times has he done it?
Nevertheless, it does matter to a hacker, who is the barber and who shaves him. This is why it is relevant to the adjudicating officer (AO) too. Let me explain.
Towards the end of the nineteenth century, mathematicians started having doubts about the foundations of their subject. They started searching rigorous proofs of their fundamentals. One area of search related to the paradoxes around self-referencing. The most famous of all such paradoxes is Epimenides or liar's paradox? Epimenides (ऍपीमेनेडीज़) was the 6th century Greek philosopher. He was a Cretan. He made an immortal statement:
‘All Cretans are liars’.
It is like, my saying,
'All Indians are liars'
Try analysing it: if you accept it as true, it boomerangs that it is false; If you take it to be false, it backfires that it is true.
A century ago, the Epimenides paradox was reformulated by Bertrand Russell as 'Barber's or Russell's paradox':
'The only barber in the village declared that he shaves only those who do not shave themselves'.
There was no problem with it, till the question is asked,
‘who shaves the barber?’
Russell and Whitehead tried to sort it out in ‘Principia Mathmatica’ a giant opus published in 1913. They thought that they had sorted it out but alas, they did not.
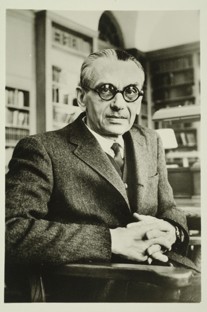
Kurt Gödel wrote a paper in 1931. It was in German and its English translation was titled 'On formally Undecidable Proposition of Principia Mathematica and Related Systems'. Gödel solved such paradoxes forever. He proved that it cannot be solved: The basic idea of the paper was,
'Proof of arithmetic consistency is not possible―every system is incomplete.'
 This has wide implications and one of them is that there is no fort that cannot be breached; and there is no computer that cannot be hacked―every system, every computer can be hacked.
This has wide implications and one of them is that there is no fort that cannot be breached; and there is no computer that cannot be hacked―every system, every computer can be hacked.
Kurt Gödel – picture courtesy Institute of Advanced Studies, Princeton
It was this idea that was subtly applied in the film, 'Independence Day' to introduce a virus in the computer of the alien ship to let down its protective shield so as to make an opening and insert a bomb inside it.
In substance, irrespective of the security measures, there will always be room for improvement. And Security measures will never be sufficient: they are to be backed up with adequate legal sanctions. The Information Technology Act 2000 (the IT Act), the most important cyber law enactment, does it by requiring safety measures to be taken and by providing penalty for its breach.
ADJUCATING OFFICER―CHALLENGES AND ROLE
Jurisdiction
Civil Nature Penalty
Penalty is a wide term with many shades of meanings. It involves idea of punishment―either corporal or pecuniary, civil or criminal―although its meaning is usually confined to pecuniary punishment. A fine is always a penalty but penalty is not always fine. It is in this broad sense that the word 'penalty' has been used in the IT Act.
Penalty as a penal measure―be it imprisonment or a fine―is to be dealt by the regular criminal courts. Penalty as a civil measure―compensation to the person affected or execution of non-compensatory amount for breach of statutory obligation―is to be dealt by the adjudicatory officers.
Compensation to the person effected for damage to the computer system etc. is provided under section 43 of the IT Act. The scope of this section is very wide. It includes illegal access and downloading, virus attacks, adware and spyware, DoS attack, illegal destruction or deletion of files, charging the services availed by a person to the other account holder.
A person illegally obtaining data stored in computer resources is liable to compensate under section 43 of the IT Act and the person maintaining the data is liable to pay compensation under section 43A if:
-
He is negligent in implementing and maintaining reasonable security practice; and
-
It results into causing wrongful loss or wrongful gain to any person;
The compensation is to be paid to the affected person. Sections 66 and 72-A fix criminal liability for the aforesaid actions.
Sections 44 and 45 of the IT Act provide penalty for failure to furnish information return etc. and for contravening any rules and regulations under the Act. This penalty is for breach of statutory obligation under the IT Act. It is exaction of non-compensatory amount but it is not a fine: it is not as a result of prosecution of an accused for committing an offence.
The adjudication officer are not concerned with criminal proceeding or penalty by way of fine in criminal proceeding. It is for this reason that rule 4(l) of the Information Technology (Qualification and experience of Adjudicating Officer and Manner of Holding Enquiry) Rules 2003 (the AO Rules) explains that the cases requiring punishment instead of financial penalty are required to be transferred to the Magistrate concerned.
Pecuniary and Territorial
The adjudicating officer has pecuniary jurisdiction up to Rs. 5 crore {Section 46(1), (1-A) IT Act}. The jurisdiction beyond the pecuniary limit lies with the competent court.
The territorial jurisdiction of adjudicating officer extends to the State or the Union Territory of his posting over contravention involving computer or computer system or computer network situate within that State or union territory. {(Rule 4 (a) and (b) of the AO Rules read with section 75(2) IT Act}.
Procedure
The penalty is to be determined after giving reasonable opportunity to the person affected and {section 46(2) of IT Act} and by following the procedure as prescribed in the AO Rules.
The AO may also get the matter investigated from an officer in the officer of controller or Indian Computer Emergency Response Team (CERT-IND) or from the concerned Dy SP. {Rule 4(i) of the AO Rules}.
The AOs can take assistance of any licensed or recognised certifying authorities, the controller and other officers in his office, agencies established under the Act and Government agencies, who are required to assist the AOs {Rule 12 of the AO Rules}.
Powers
Section 4 and rule 5 of the AO Rules indicate that while deciding the quantum of compensation or penalty, the AO is to have due regard to the following factors:
-
The amount of gain of unfair advantage;
-
The amount of loss caused to the person as a result of default;
-
Repetitive nature of the default.
The AO has the same powers as the civil courts, while deciding the cases, in respect of the following matter: {section 46(5) read with section 58(2) and Rule 3 of the Information Technology (others powers of Civil Court vested in Cyber Appellate Tribunal Rules, 2003}:
-
Summoning and enforcing the attendance of any person and examining him on oath;
-
Requiring the discovery and production of documents or other electronic records;
-
Receiving evidence on affidavits;
-
Issuing commissions for the examination of witnesses or documents;
-
Reviewing its decisions;
-
Dismissing an application for default or deciding it ex parte;
-
Setting aside any order of dismissal of any application for default or any order passed by it, ex parte;
-
Requisitioning of any public record, document or electronic record from any court or office.
For smoothly conducting the proceedings, the AOs are also empowered as follows:
-
All proceedings before them are deemed to be judicial proceeding within meaning under section 193 (Punishment for false evidence) and 228 (Intentional insult or interruption to public servant sitting in judicial proceeding) IPC {Section 46 (5)(b) IT Act}.
-
They are also deemed to be civil court for the purposes of section 345 (Procedure in certain cases of contempt) and 346 (Procedure where court considers that case should not be dealt with under section 345) CrPC. {Section 46(5) ( c) IT Act}.
Any contravention under the IT Act can also be compounded by the AO but this can only be done once in three years. (Section 63 of the IT Act read with Rule 11 of the AO Rules).
The amount determined by the AO can be recovered by two methods:
-
The penalty can be recovered as arrears of land revenue (section 64 of the IT Act).
-
The damages to the person affected can be recovered as a decree of the civil court is executed. This is clear from Section 46(5)(c) which provides the AO to be a civil court for purposes of order 21 CPC.
CONCLUSION
 I started my talk with reference to a paradox. Let me end with a paradox ― the paradox of cyberspace and the Internet.
I started my talk with reference to a paradox. Let me end with a paradox ― the paradox of cyberspace and the Internet.
Cartoon – courtesy Wikipedia
Peter Steiner published a cartoon in the New Yorker on 15th July 1993: a milestone in many ways. Two dogs with the computer. The dog sitting in front of the computer keyboard telling the other,
'On the Internet, nobody knows that you are a dog.'
This is the paradox of Internet; it is the paradox of Cyberspace. This is also the genesis of contraventions in cyberspace. People are emboldened to commit it because they mistakenly assume that they are anonymous but this is not correct.
Well, the truth is, on the Internet, everybody knows that you are a dog. There is nothing private in the cyber space: it is the end of privacy.
Not all cyber crime is reported. This is not only true in the case of individuals but also in the case of the corporations. This could be because of lack of the confidence in the people. It is good that this seminar with the adjudicating officers is organised. This will help them in deciding cases related the contraventions in cyberspace quickly and satisfactorily, boosting the public confidence.











